analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
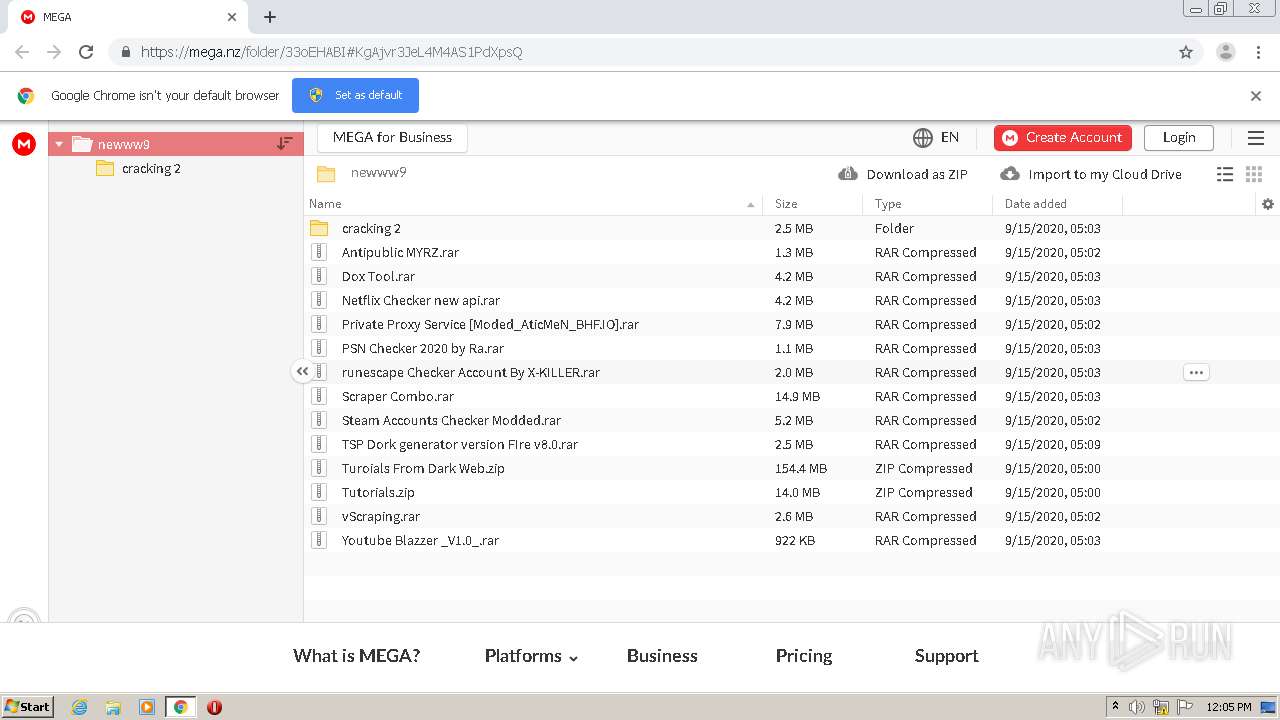
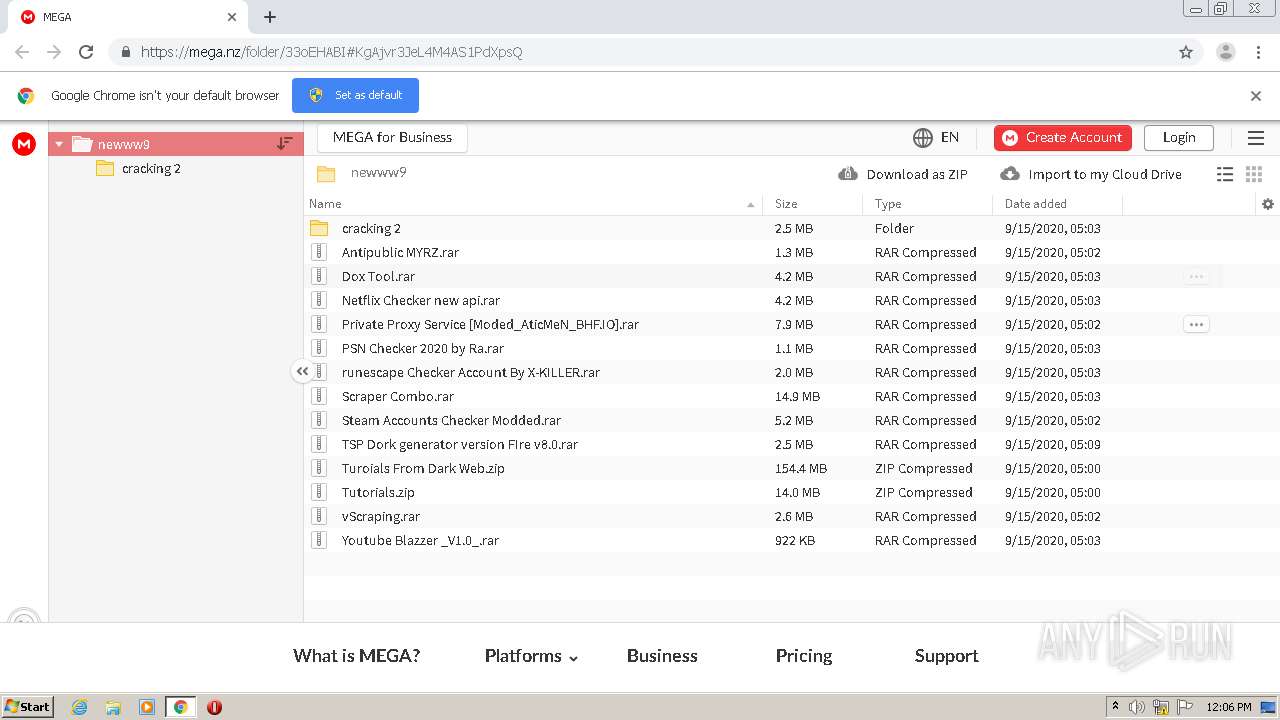
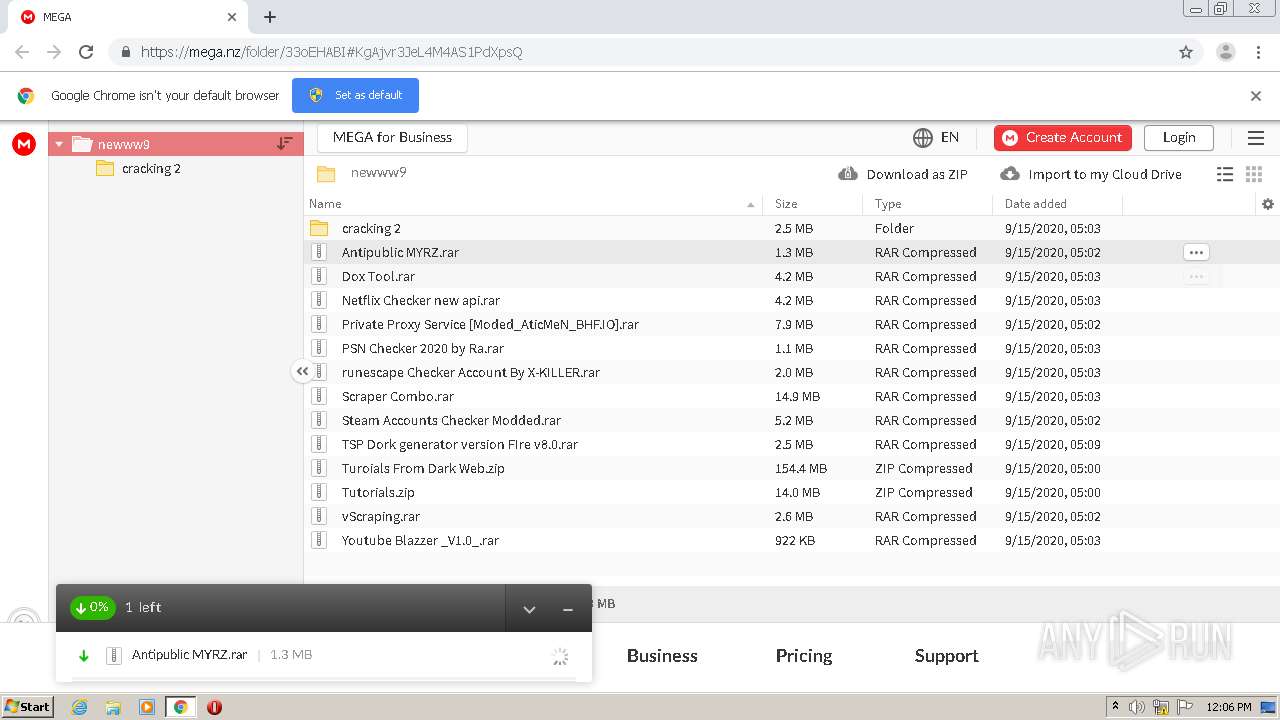
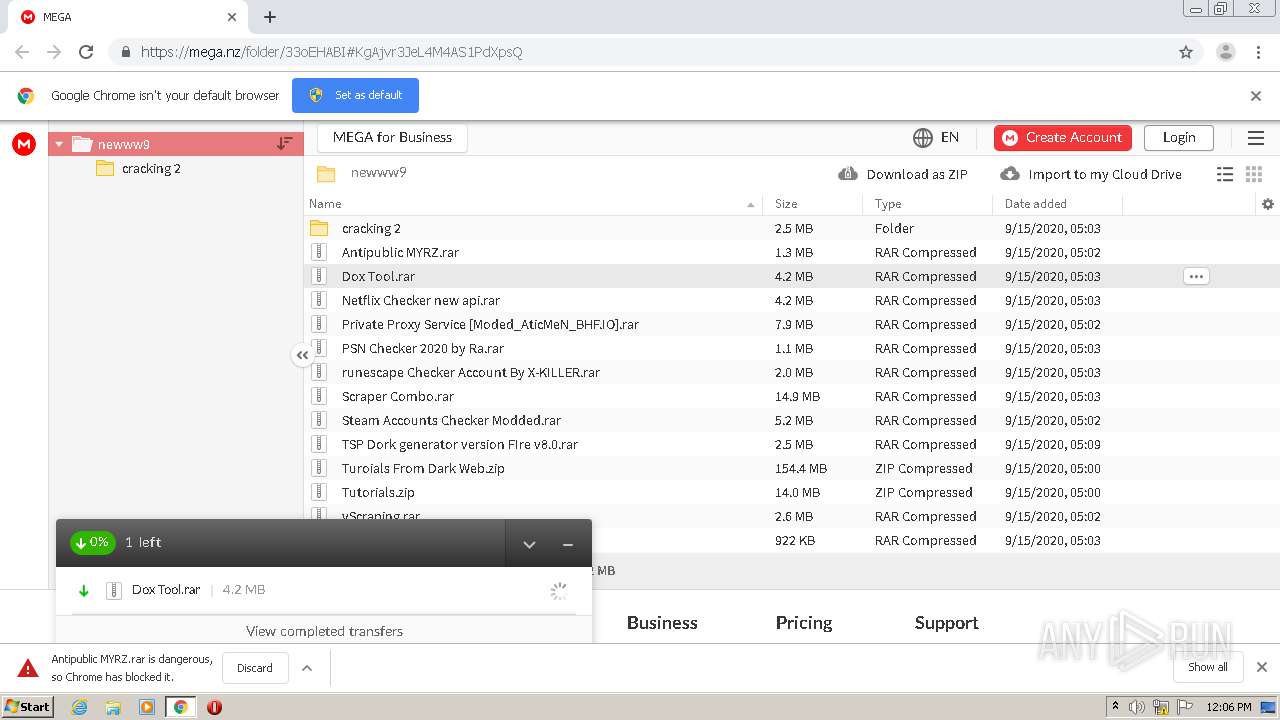
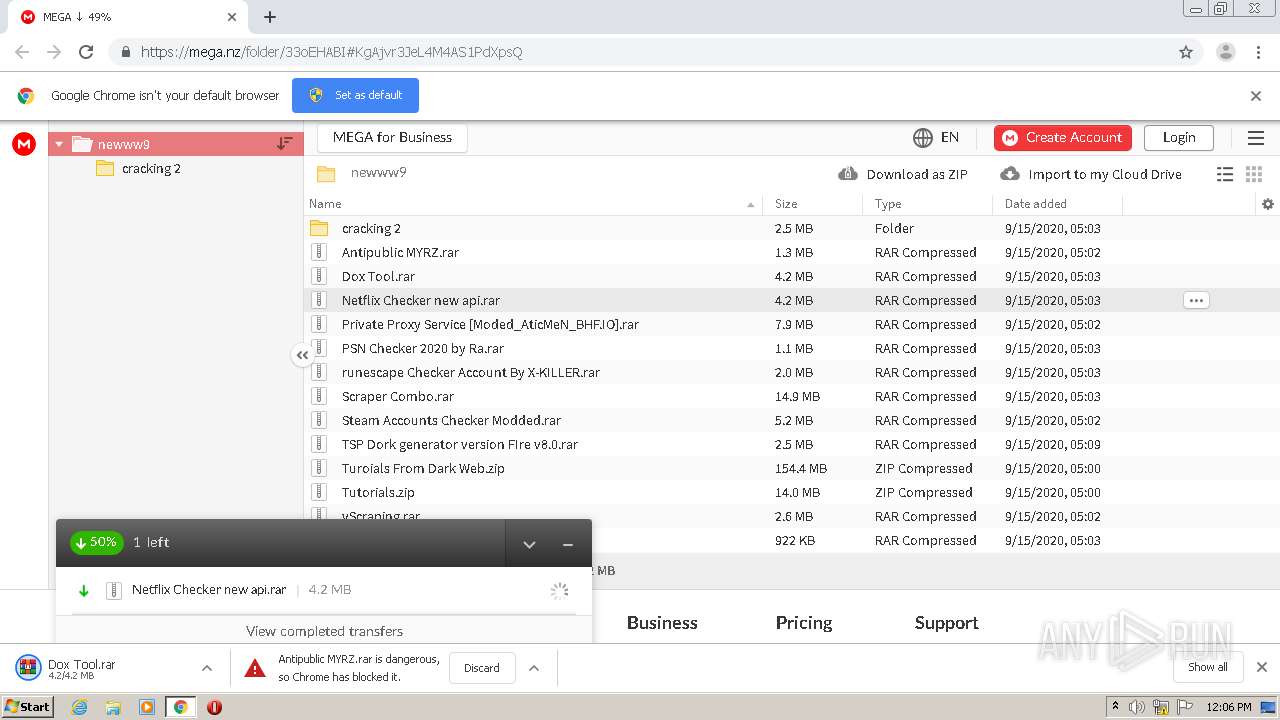
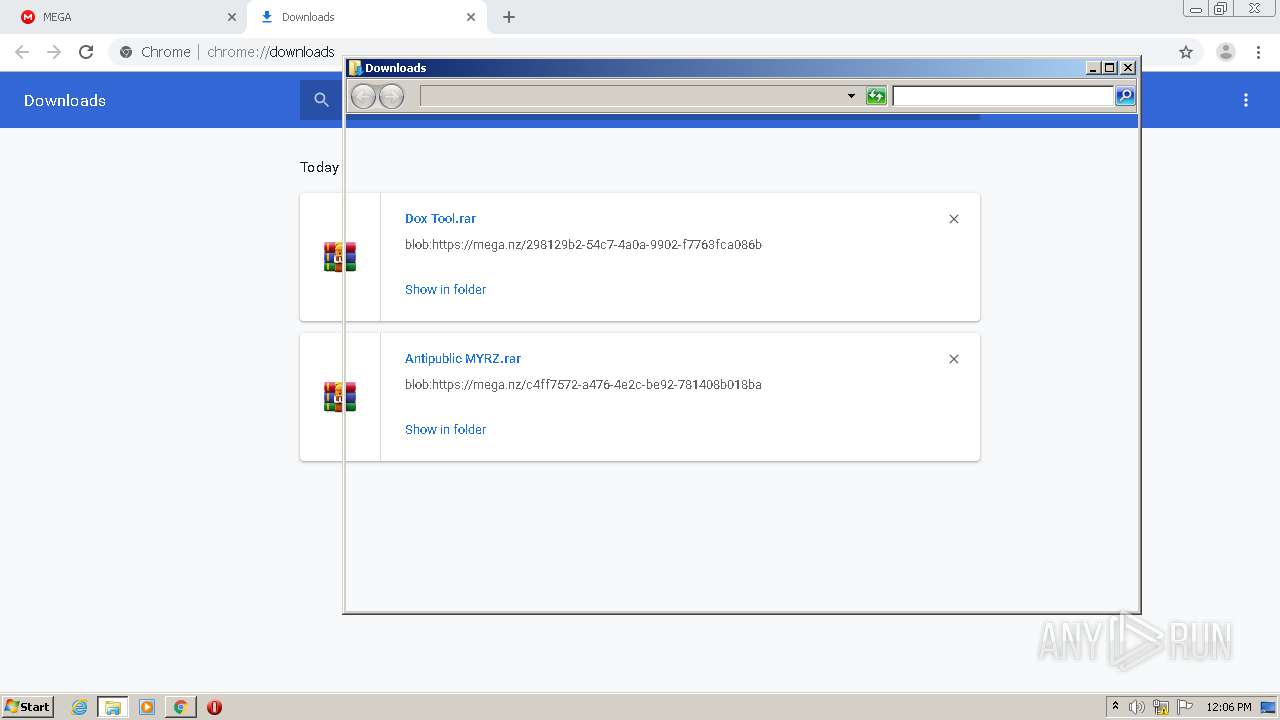
| URL: | https://mega.nz/folder/33oEHABI#KgAjvr3JeL4M4AS1PdXpsQ |
| Full analysis: | https://app.any.run/tasks/f35d1930-ac35-4581-99a1-0a2498b58d49 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2020, 11:05:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D12BF4F196C554F08D6BDEFACE93E46 |
| SHA1: | 1029B1A2475C536E52FC892D5487D88E34FF55F1 |
| SHA256: | 45181C733A8C6C0E0C17737D365DEF51B054C2C2133FA38EB7CA4EAB3F753588 |
| SSDEEP: | 3:N8X/iuyKWytknLMSUL9l:26Nytk/gD |
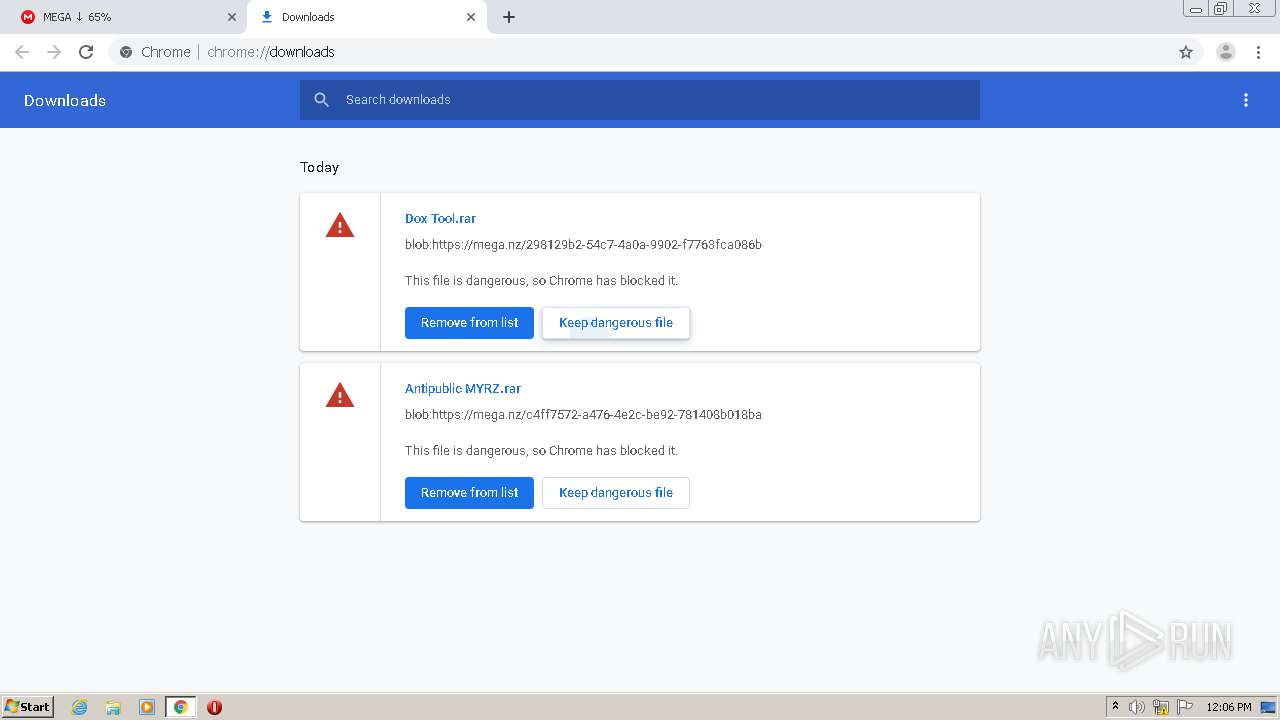
MALICIOUS
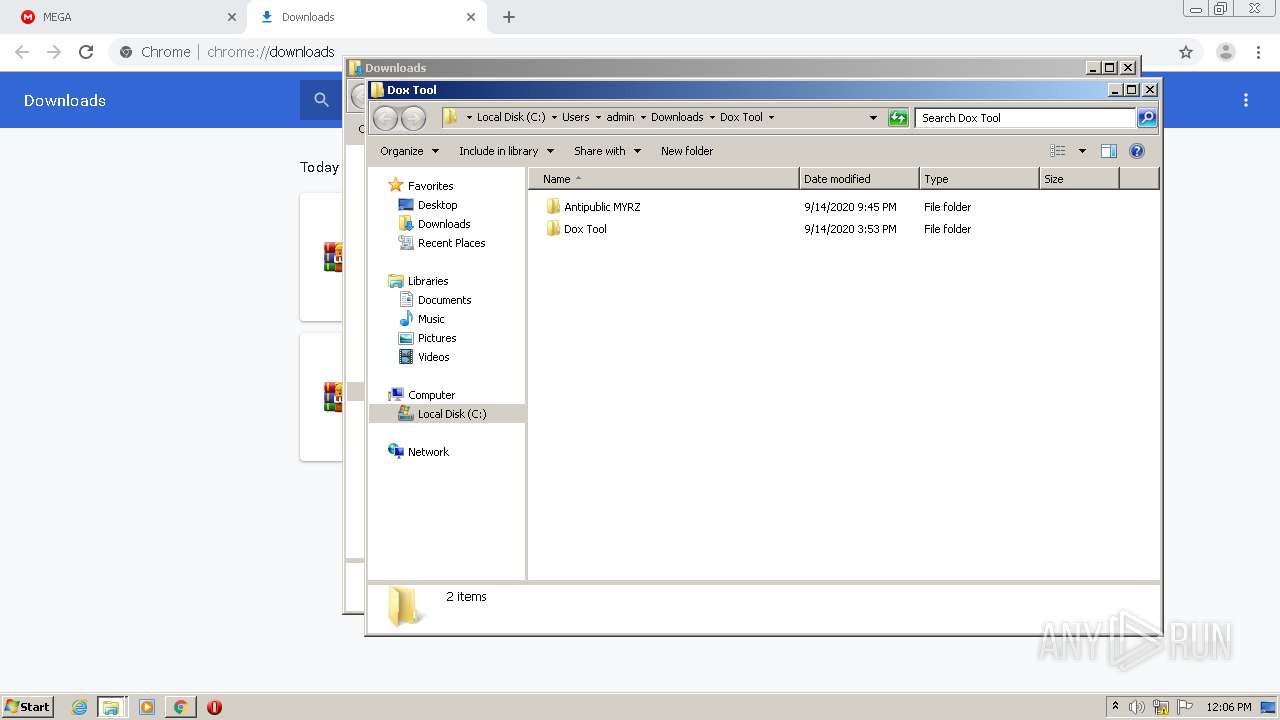
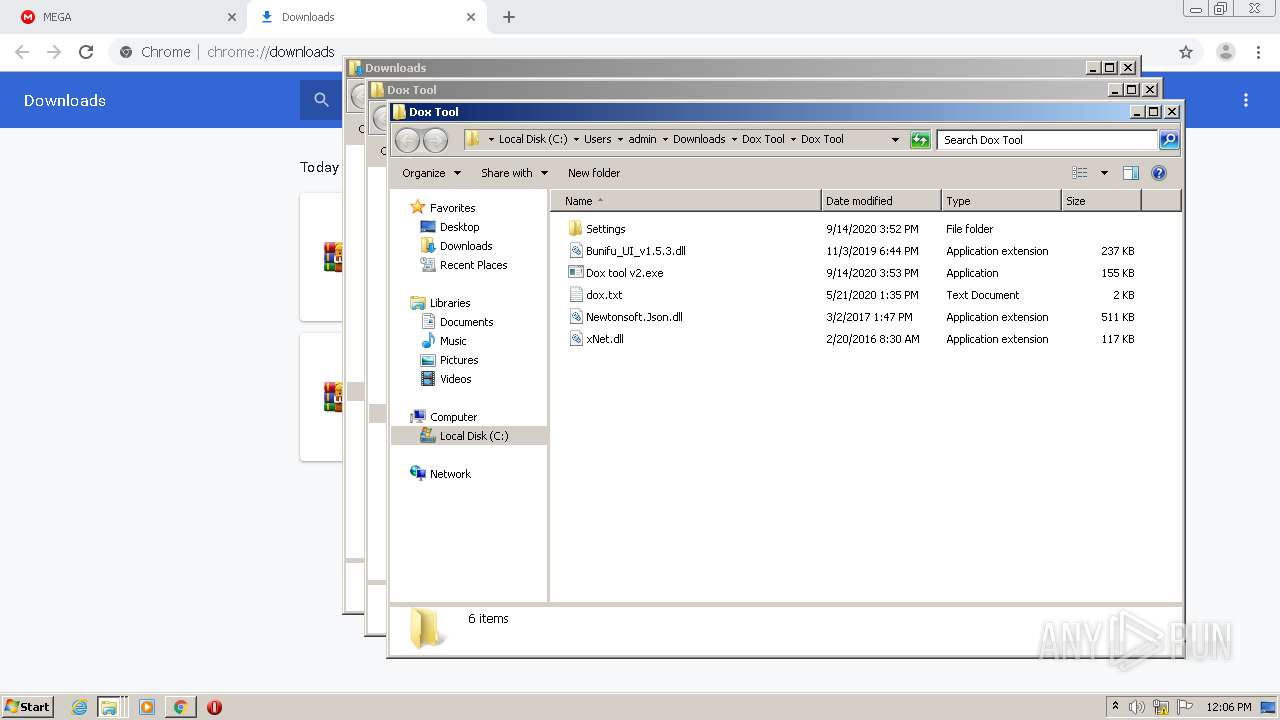
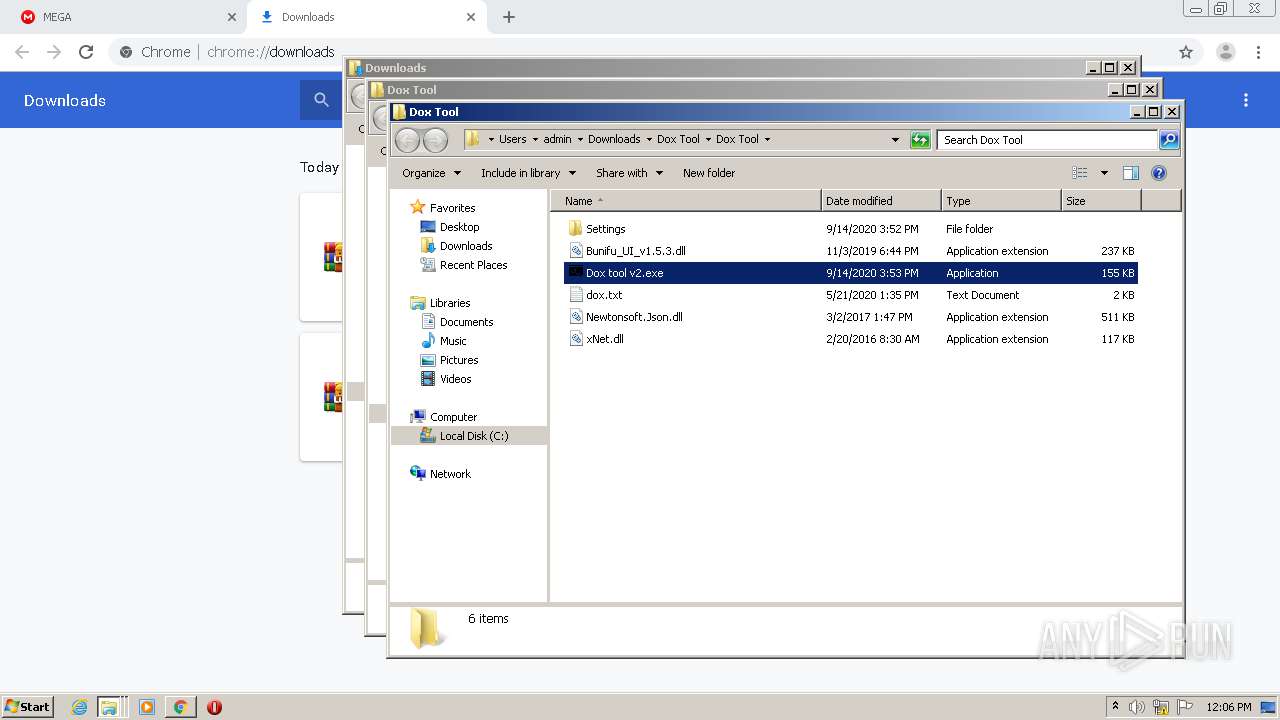
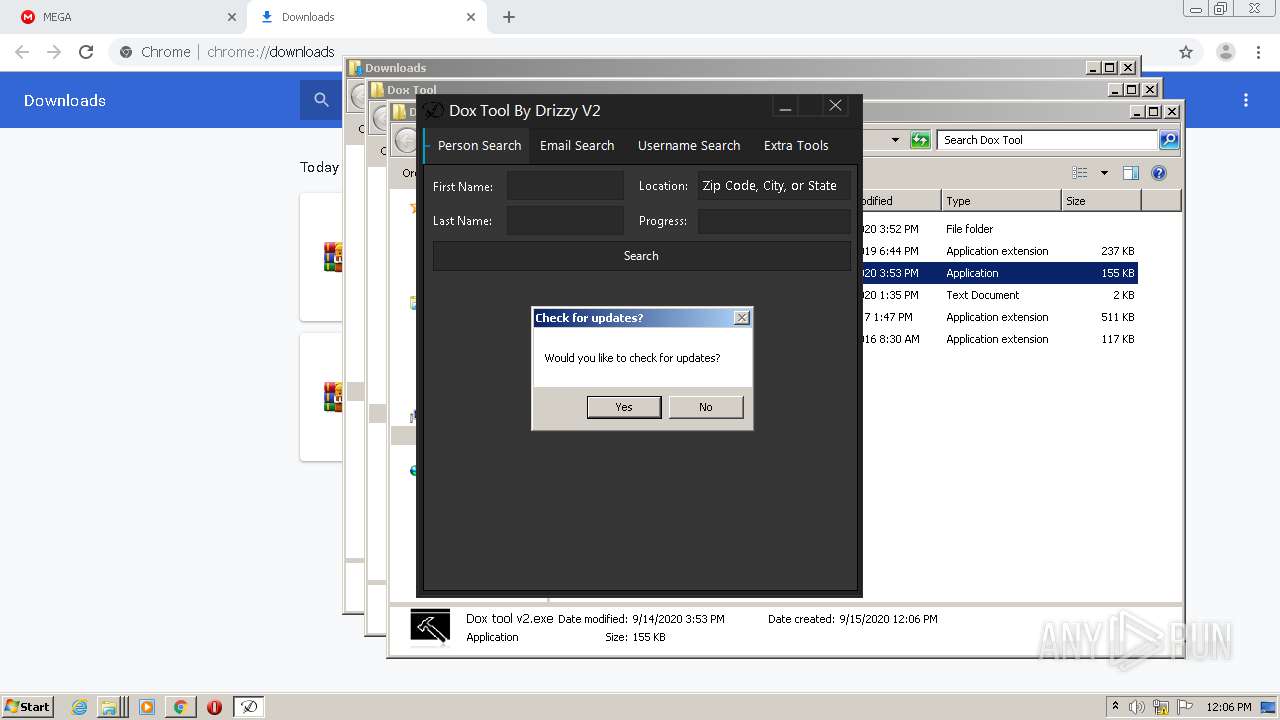
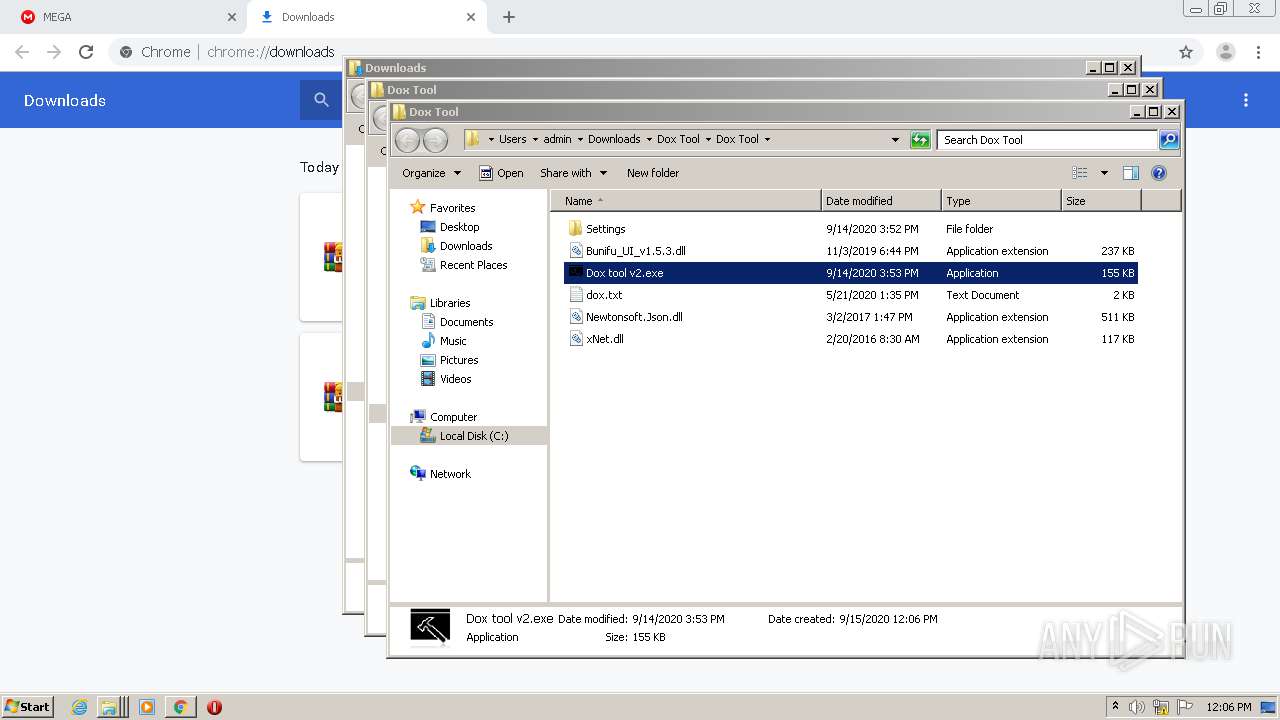
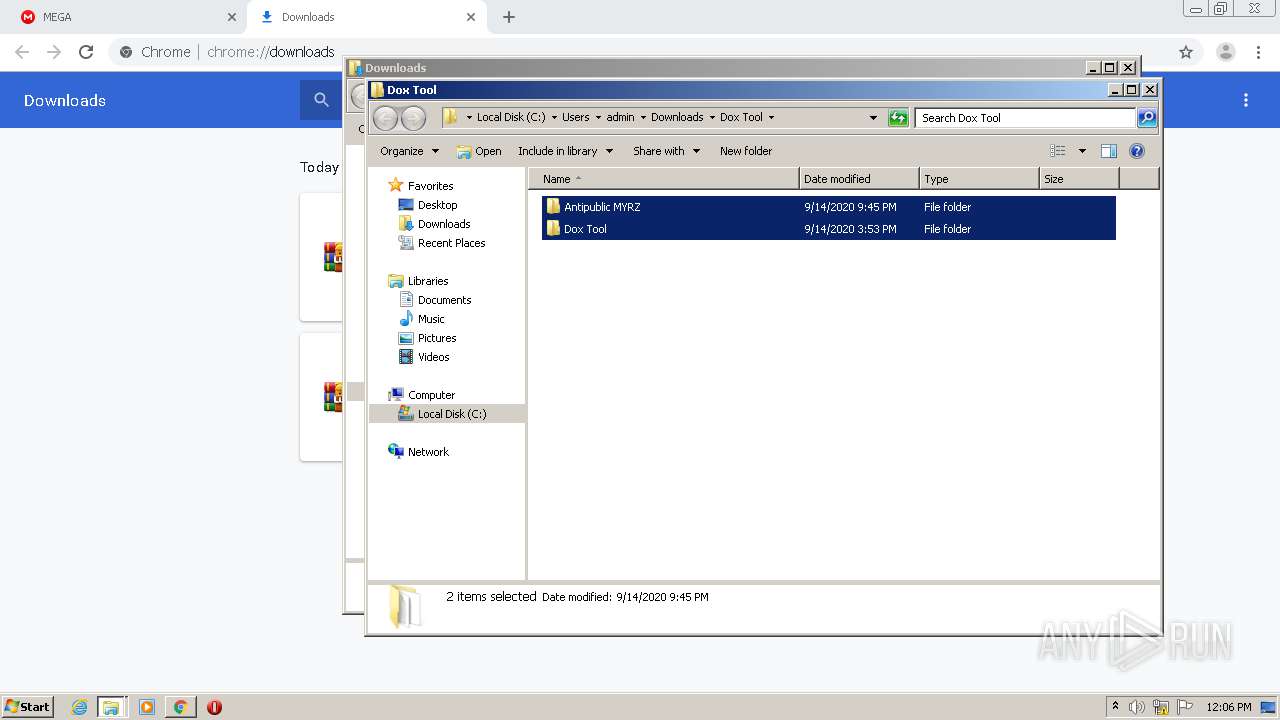
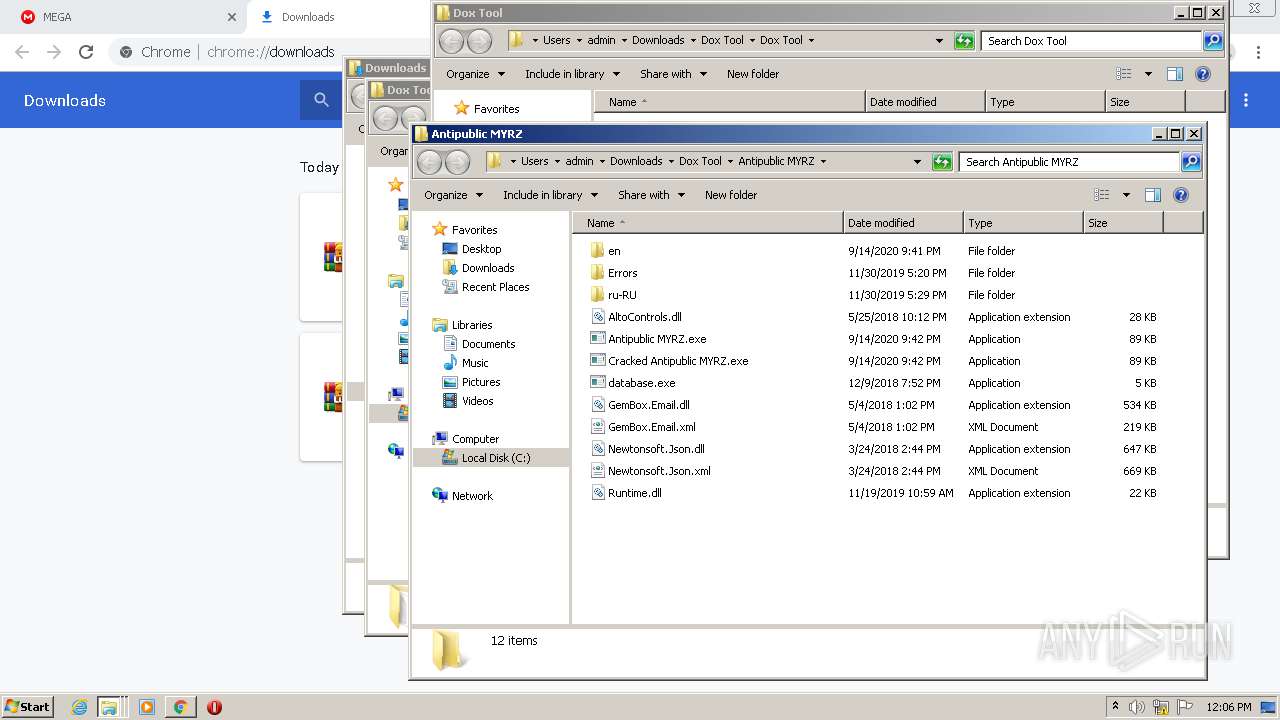
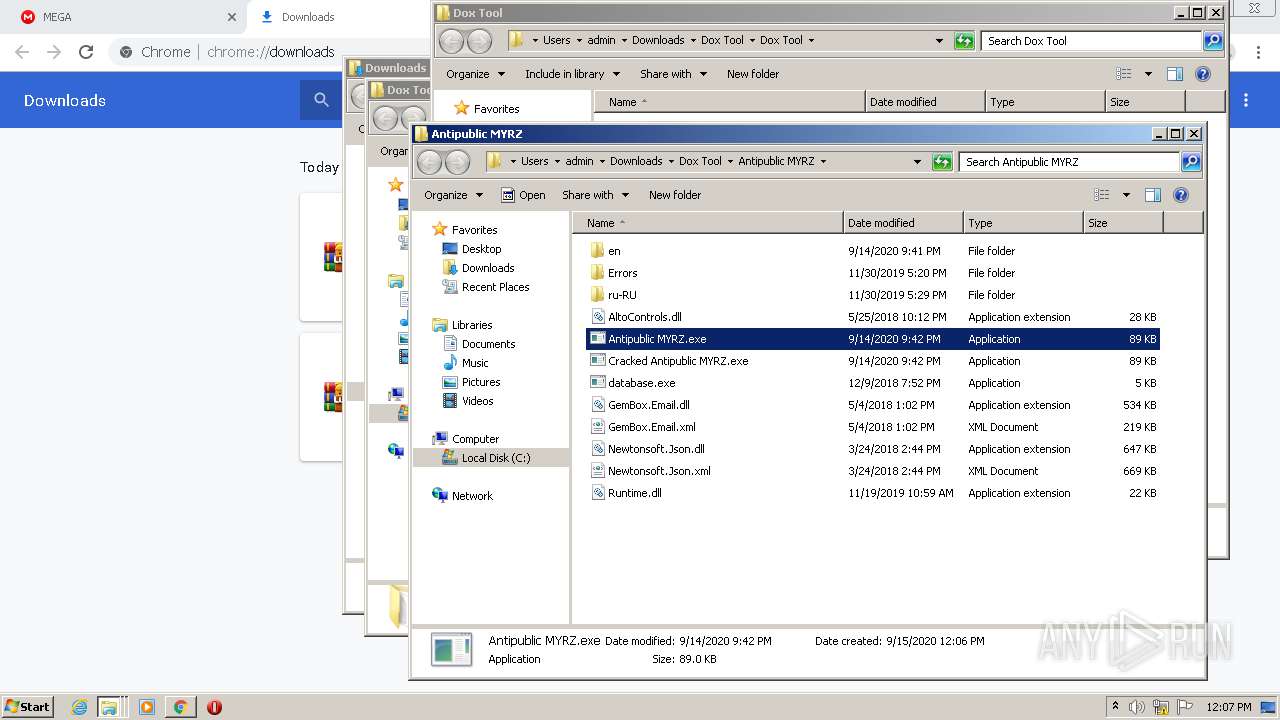
Application was dropped or rewritten from another process
- Antipublic MYRZ.exe (PID: 2088)
- ctfmom.exe (PID: 1688)
- Dox tool v2.exe (PID: 1256)
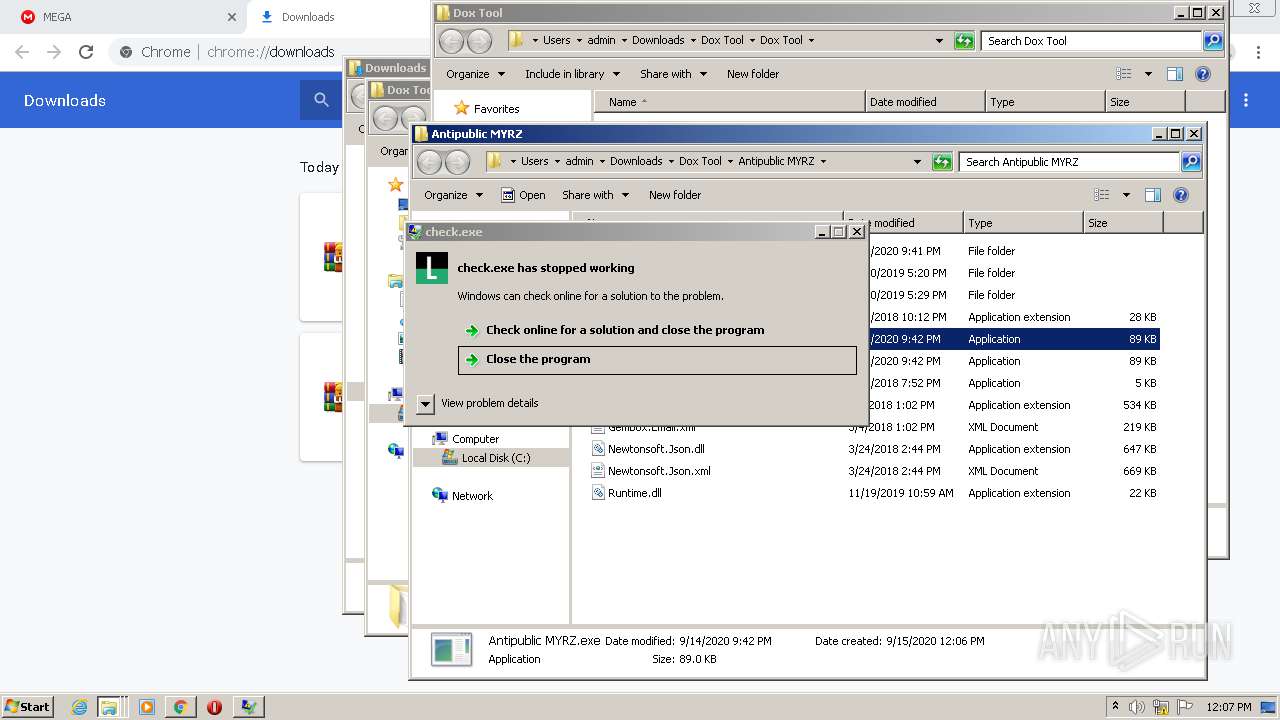
- check.exe (PID: 3228)
- settings.exe (PID: 1948)
- check.exe (PID: 2840)
- runtime.exe (PID: 2560)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 4052)
- check.exe (PID: 2840)
Writes to a start menu file
- check.exe (PID: 3228)
SUSPICIOUS
Creates files in the user directory
- check.exe (PID: 3228)
Starts CMD.EXE for commands execution
- Dox tool v2.exe (PID: 1256)
- Antipublic MYRZ.exe (PID: 2088)
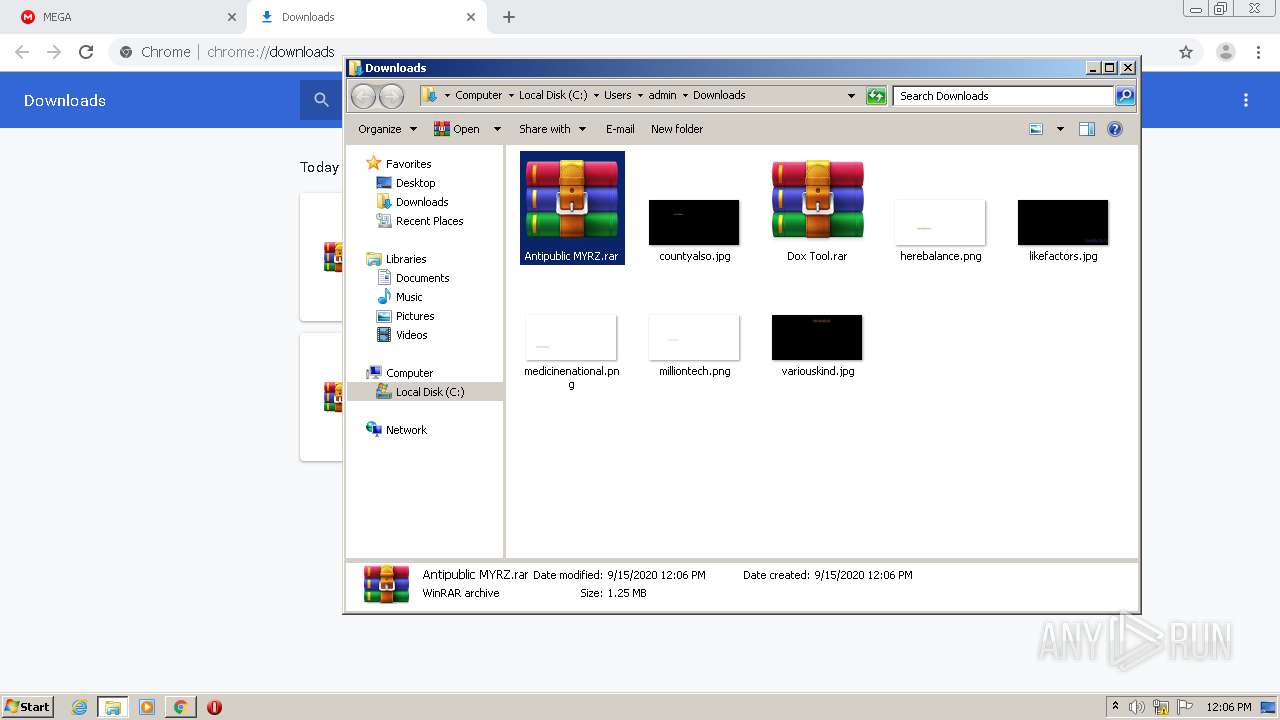
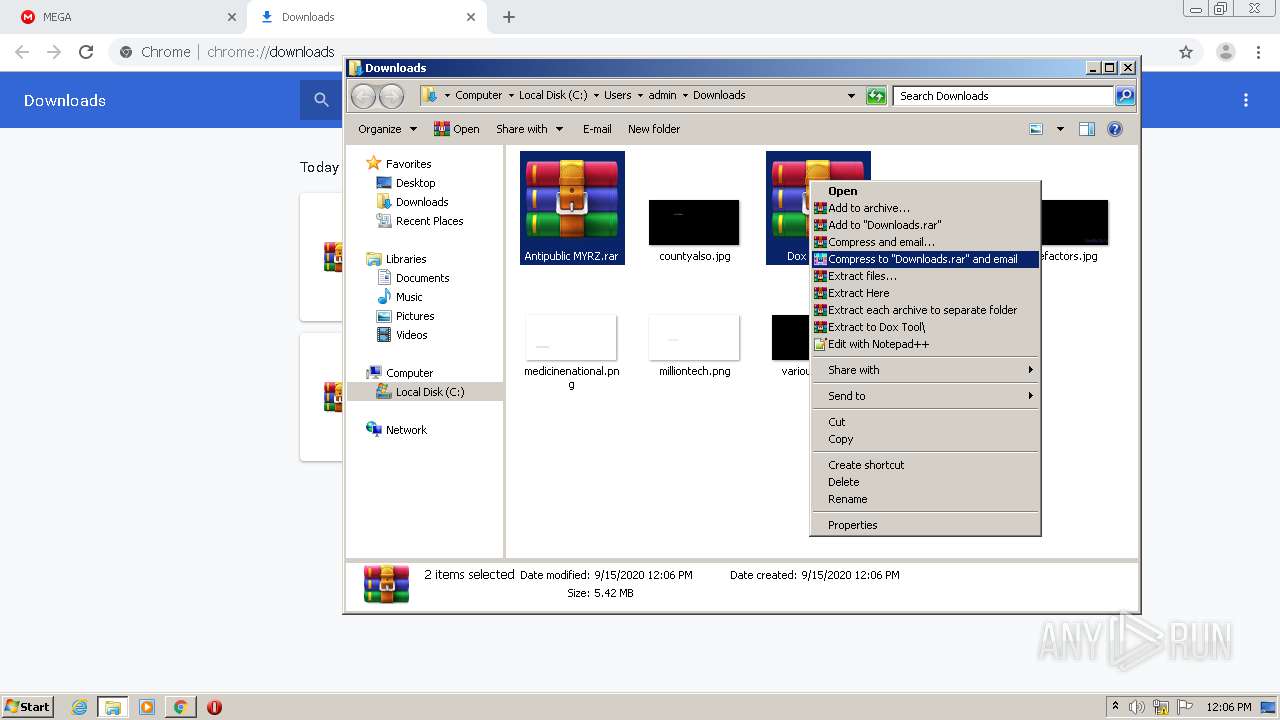
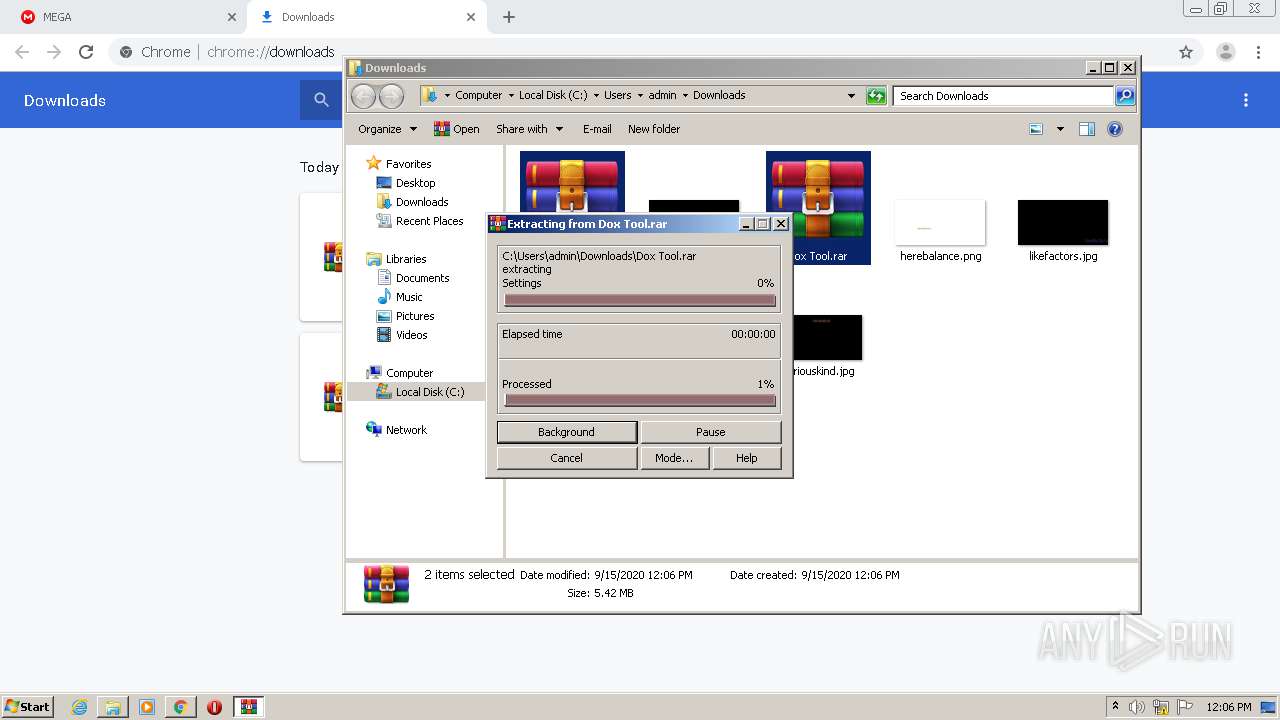
Executable content was dropped or overwritten
- check.exe (PID: 3228)
- WinRAR.exe (PID: 2744)
- check.exe (PID: 2840)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2832)
INFO
Reads the hosts file
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2832)
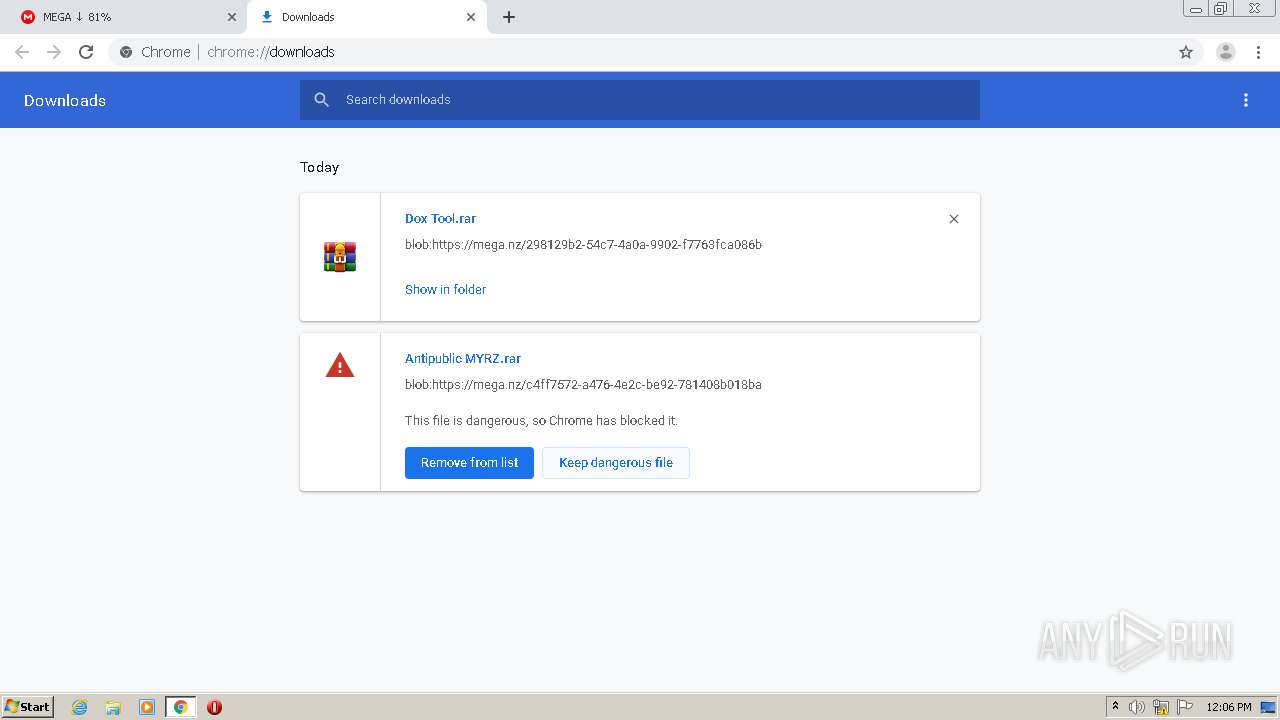
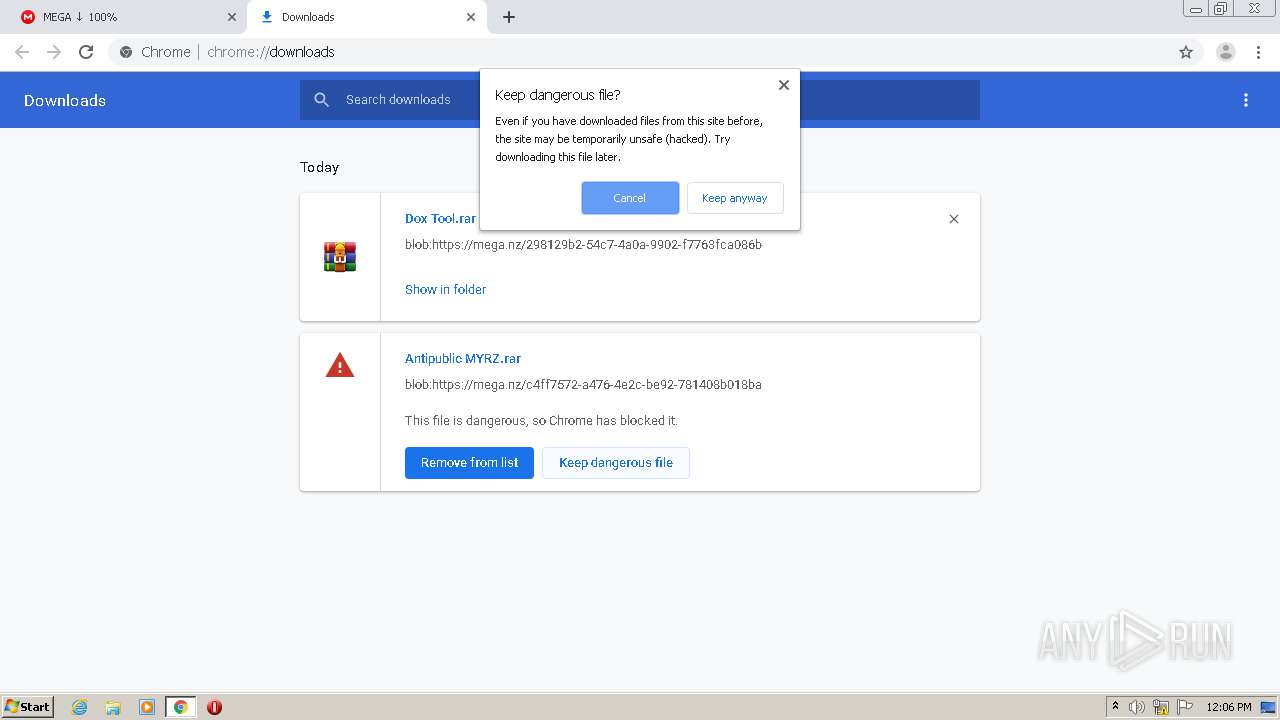
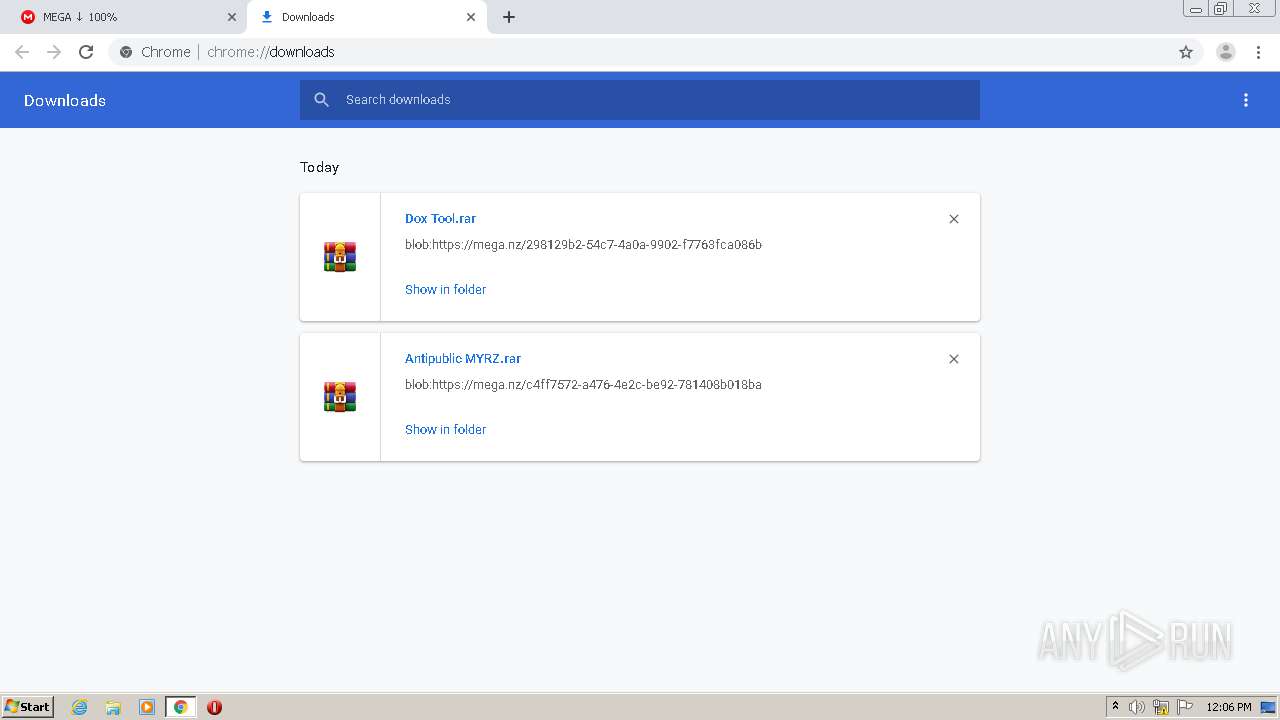
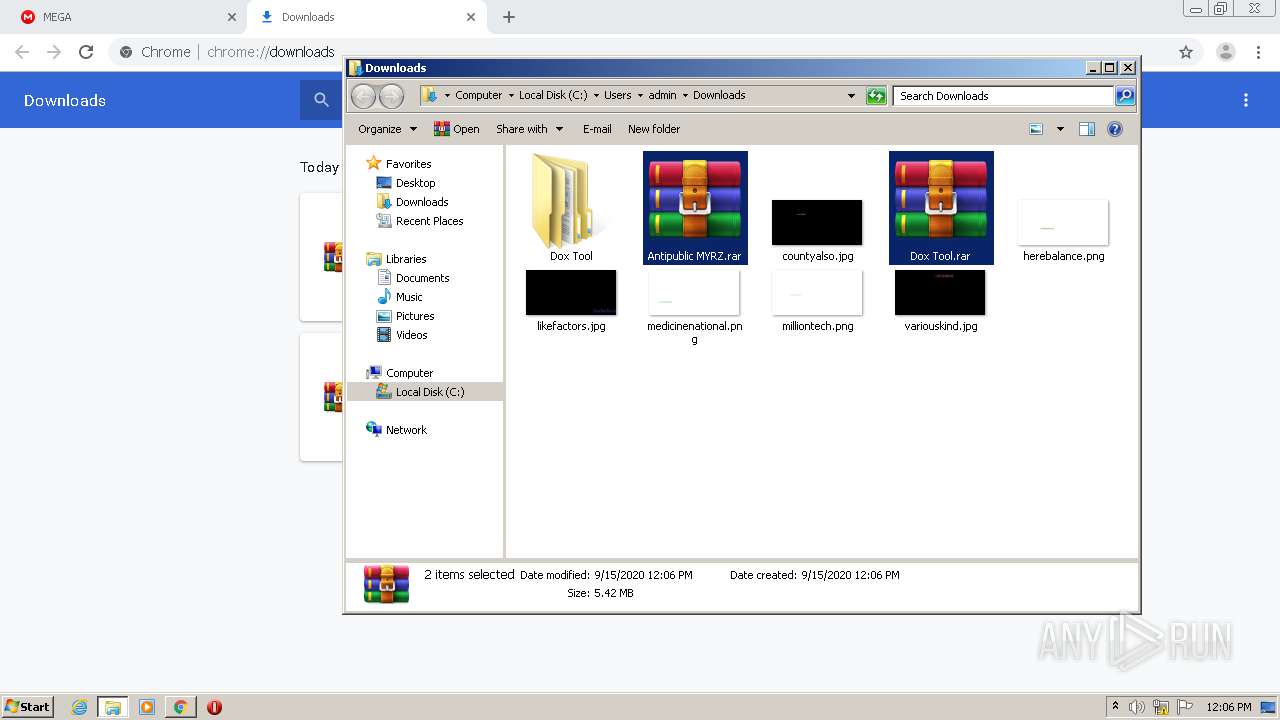
Manual execution by user
- WinRAR.exe (PID: 2744)
- Antipublic MYRZ.exe (PID: 2088)
- Dox tool v2.exe (PID: 1256)
Dropped object may contain Bitcoin addresses
- check.exe (PID: 3228)
- WinRAR.exe (PID: 2744)
Application launched itself
- chrome.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
32
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://mega.nz/folder/33oEHABI#KgAjvr3JeL4M4AS1PdXpsQ" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x7141a9d0,0x7141a9e0,0x7141a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2736 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 4012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=716875010645413630 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=661342870976617062 --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7483270743274140555 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13005474963237574139 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1355517598954519540 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10976772624080682217 --mojo-platform-channel-handle=3728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9998904615466346631 --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
1 780
Read events
1 671
Write events
0
Delete events
0
Modification events
Executable files
51
Suspicious files
45
Text files
165
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6d6fdb76-29e5-4499-bcea-f0003d658a68.tmp | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:0CE1FA0314D44178816BA5E7133E07DD | SHA256:8D81EC8C4EFED885A0FF9267B0B388FB53316938EEDCDFABDC697E3610883714 | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:142AFC7F980CB38310D0680F2E8907CF | SHA256:3D5E5DF95E28CF65C77882748077EC52706AF02F8D869E188B6D16F782F82F44 | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF26e4b9.TMP | text | |
MD5:142AFC7F980CB38310D0680F2E8907CF | SHA256:3D5E5DF95E28CF65C77882748077EC52706AF02F8D869E188B6D16F782F82F44 | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF26e48b.TMP | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | gmc | |
MD5:B6D81B360A5672D80C27430F39153E2C | SHA256:30E14955EBF1352266DC2FF8067E68104607E750ABB9D3B36582B8AF909FCB58 | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF26e48b.TMP | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
53
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2252 | chrome.exe | GET | 200 | 173.194.187.232:80 | http://r3---sn-4g5ednly.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=89.187.165.47&mm=28&mn=sn-4g5ednly&ms=nvh&mt=1600167797&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
2252 | chrome.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2252 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 172.217.23.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 31.216.148.10:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
2252 | chrome.exe | 66.203.127.11:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
2252 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 216.58.212.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
www.google.com |
| whitelisted |
g.api.mega.co.nz |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |